Hundreds of physical keys get lost, stolen, or copied.
It means you have zero real-time control over sensitive data, expensive inventory, and visitor management.
If you want the right people in the right place at the right time, it’s time for badge access control systems.
These badge systems allow for single-tap or wave access for employees or visitors at the main gate, across multiple floors, and even across different sites.
Badges verify who is allowed where. You are not only allowing entry but also restricting it to sensitive areas of your premises to help keep them secure from unauthorized access attempts.
If you look for workplace security and speedy visitor management across departments and even across different sites, this is exactly what we discuss in this blog: the badge access control system: how it works, its advantages and disadvantages, and alternatives to the badge access control system.
What is a badge access control system?

A badge access control system is an electronic security system that uses RFID badges, key cards, or small key fobs to verify identity. You swipe these cards across the badge reader, and the reader grants or denies access to buildings, departments, or restricted areas.
Depending on the level of security and convenience, it’s an entry system that relies entirely on RFID badges for electronic access.
| Steve Vieira, Google’s security systems director, believes: “Physical ID badges are still very important. According to him, badges are essential because they build trust, align with company culture, and comply with legal or regulatory requirements.” |
He reinforces an important point: badge systems remain a trusted foundation in modern security. That’s what we picture in an ideal modern office security system. With speedy, single-tap verifications, employees can move through secure areas.
Here’s how organizations maintain structured access permissions and digital logs across different industries:
- Schools and K-12 campuses.
- Temporary and permanent access at construction sites.
- Multi-family residential entrance and special security at shared spaces(gyms, pools, fitness clubs)
- Industrial and manufacturing facilities.
- Truck yards.
What are the components of modern badge systems?
A badge access door system consists of the following technologies:
ID badges:
Contain employee info, a photo, or a unique ID.
Card readers:
Authenticate badges at doors, elevators, or restricted zones.
How does the badge access control system work?
Badge access control systems verify credentials to determine whether entry should be granted or denied. This contactless entry system lets you issue, track, disable, and retrieve employee access electronically. The process is simple yet powerful, especially when combined with modern badge technologies such as RFID.
Step 1: Credential verification:
- Employees present their badge to a reader.
- The system checks the badge information against a secure database.
- Access is either granted, and the door unlocks. If the access is denied, an alert is triggered.
Step 2: Badges and readers:
RFID badges are one of the most common and convenient types of employee badges. You can easily design, manage, and print badges with access credentials:
- Employees tap or wave their badge near an RFID reader.
- Radio waves transmit data from the badge to the reader, instantly verifying identity.
- Typical ranges vary from a few inches to several feet, allowing for convenient, contactless entry even from a car in a parking lot.
Sol, let’s find out if your business needs a badge access system:
When does your business need a badge access control system?
If you have a small to medium-sized enterprise, badge-based access control systems can secure assets and simplify employee management.
1. Protect sensitive areas:
If you want unmanned security server rooms, labs, R&D departments, or storage areas with valuable equipment or confidential data.
2. Monitor inter-departmental movement:
When employees move between floors, departments, or semi-restricted zones, you want to be sure about after-hours access, prolonged stays, or unauthorized cross-departmental movement.
3. Automate attendance and timekeeping:
You want to track shift start and end times automatically and integrate with payroll systems for accurate, real-time reporting.
Types of employee badge entry systems and their applications:
It is not just about entering a particular turnstile, elevator, or parking garage. You decide access based on roles. You maintain full control by using it as a tool to manage movement, control resources, and monitor behavior throughout your facility. Here are different technologies that can be embedded on the badge:
RFID badges:

RFID badges are available as classic PVC cards, fobs, or adhesive tags. They are used for high-traffic areas, elevators, and department-level access.
An ultra-range high-frequency RFID badge provides a range of 10-15 meters. Their fast read speed makes them ideal for employees who frequently move between zones. It’s better to opt for cards operating at frequencies above 125 kHz (Low Frequency) because they are harder to duplicate.
Where can they be used:
RFID badges are excellent for monitoring departmental movement and enabling real-time alerts. Fast contactless scanning makes them ideal for tracking employees across floors, zones, or restricted areas without slowing down operations.
Swipe badges:
Magnetic stripe badges are easy to update and reassign, making them suitable for dynamic roles or temporary staff. They can control access to restricted departments, office equipment, or resource rooms, though they require more maintenance than contactless options.
Where to use these:
Best for resource control like secure printers, workstations, server rooms, or lab equipment, especially in smaller setups
QR-code badges:
It is a cost-effective, simple-to-deploy contactless office badging system. Every scan logs the exact timestamp, location, and person, and expires after 30-180 seconds.
For example: “Sam Clinton – Main entrance – 08:00 AM”
QR code badges work well for temporary access or visitor management, such as for contractors moving between departments.
For sensitive areas, you can add biometric verification. So you unlock your phone using your thumbprint, then use the QR code. You make it safer by adding two-factor authentication.
By integrating QR scanning with real-time authentication servers, risk can be mitigated and link access logs to each individual.
Mobile badges:
Phil Coppola, HID’s mobile technology evangelist, says:
“Plastic badges will die within the next five years.”
Access badges built into smartphones allow remote distribution, instant revocation, and app-based access.
Where should you use them:
They can manage complex access hierarchies, including multiple floors, zones, and sensitive departmental areas.
| Top tip: Keep reading to learn how to integrate mobile access badges with AI video monitoring, behavioral analytics, and remote concierge systems to maximize security. |
How the badge technology secures your premises?

Real-time access to events:
The badge access technology dashboard displays a live feed of every badge scan as it happens. So you have a complete view of who entered or exited, which door and floor, and exactly when.
It also includes the person’s name, employee ID, photo (if enrolled), and whether access was granted or denied. In case of a denial, it also displays the reason, such as “invalid time window” or “unauthorized zone.” The security teams have instant awareness of all entry activity.
Occupancy and who is on-site:
It’s not just about giving access to authorized employees or visitors; it also tracks how many people are currently inside the building or specific zones.
Also, during off-hours, the security teams can see at a glance who has badge-checked in but not yet checked out. This occupancy rate tracking helps with fire evacuations and also triggers alarms if the restricted area exceeds its safe capacity.
Access permissions and schedules:
The biggest advantage of badge access systems is that you can assign and update permissions in bulk rather than one by one, for example, for new admissions in schools and colleges.
You can assign temporary credentials for visitors, such as for a seminar. You can also customize the access to time-based rules (for example, contractors are only allowed Monday to Friday, 7 am to 6 pm.
Audit logs and reports:
The badge access logs are a complete, searchable history of every access event across your facility. You can filter them by person, door, date range, or event type.
So if a supervisor comes up with specific questions like “Who accessed the server room after hours last month?” or “Show all denied attempts at the loading dock this week.”
No problem! You can even export these logs to CSV or PDF for compliance audits related to OSHA, HIPAA, FERPA, or internal investigations.
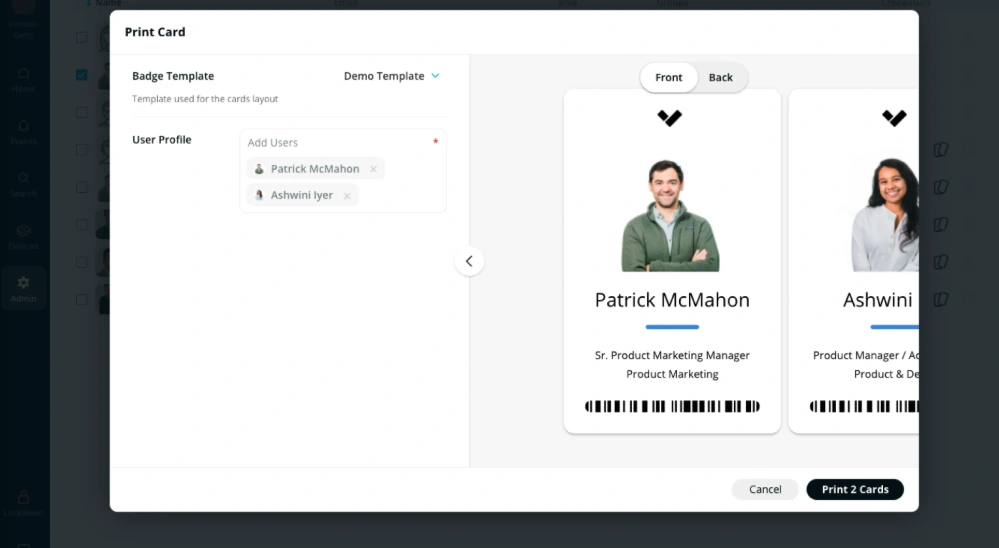
User and badge management:
This area stores employee profiles, including name, photo, department, and manager, and tracks each badge’s status as active, lost, deactivated, or expired. From here, admins can quickly issue new badges, instantly deactivate lost or stolen ones, or bulk-upload users via CSV or HRIS integration. It streamlines onboarding and offboarding, ensuring that access rights are always up to date.
System health and device status:
You have technical status of all hardware, showing which readers are online or offline, battery levels for wireless devices, firmware versions, and any communication errors between controllers and the central server.
Where can you use badge access control systems?
Badge access control systems are not just about entering a warehouse or an office building. It’s also about navigating through it.
An employee badges in at 9:02 am. Everything is valid.
From there:
- They pass through the reception.
- Take the elevator to another floor.
- Walk into a different department.
- Enter a semi-restricted area.
With badge readers at every step, you can control access at every level, across zones, and within departments.
What are the drawbacks of badge access control systems?
Badge systems can’t be trusted 100%, not because there’s a loophole in technology; they fail because they can be misused. How exactly?
- Shared credentials: “Hey, I forgot my badge. Can I use yours real quick?”
- Tailgating: “Hey, please hold the door for me. Thanks.” That’s how unauthorized individuals “tailgate” behind authorized staff.
- No real-time validation: The system approves the badge, even though the person using it isn’t the actual employee.
- No behavioral monitoring: Someone enters a restricted floor and stays there for hours; no alerts are triggered, and no questions are asked.
- No context awareness: An employee badge is used at 2 am on a weekend, and the system treats it as completely normal.
What are the alternatives to a badge access control system?
| As Xavier Cyr, our security products production manager, says: “Because a badge tells you who should enter, but not who actually did. You need to add layers of security.” |
Remote video monitoring adds active layers of protection, combining video verification, real-time intervention, and live voice talk-downs to detect and deter unauthorized activity instantly.
Video surveillance topped up with advanced AI video analytics:
The first layer of security that you can add is AI security cameras. Because a badge proves access but not identity, video proves both. Strategic partnerships manager Connor Chavarria says:
“When access control, CCTV, and visitor systems talk, one update handles it all, saving hours of admin each week.”

Stops the nuances of tailgating people and cars:
Video surveillance provides visibility, validation, and quick response times. When someone follows an authorized user, the system triggers a tailgating alert. The AI security camera detects a tailgating vehicle or person at the gate and triggers alarms. Add to that strobe lights and a quick voice intervention by live operators.
Loitering detection:
AI security cameras are now an integral part of an access control system. These security cameras installed at the gates detect loiterers in the vicinity of your perimeter, immediately before they even attempt a false badge entry.
Remote concierge:
If your visitor management system needs a human touch, consider a remote concierge, delivered at a higher standard than traditional remote video monitoring.
Remote Concierge is a modern visitor management service that uses live video, two-way audio, and a remote operator. As soon as the visitor arrives, operators respond to events such as door sensors or analytics alerts. They interact with visitors to obtain credentials, verify identities, and grant entry upon verification.
This cloud-based access control is efficient for industries such as condos, offices, transportation, and car dealerships.
Remote gate access control:
Remote gate access control is not just about opening or closing doors; it’s about decision-based entry.
As soon as the visitor presses the intercom button on the gate, the system handles access backed by real-time intelligence and a human operator. Instead of blind access, a trained operator runs predefined protocols, verifies context, and takes action. Every gate interaction is a controlled security event.
The real shift, however, comes from combining gate control with video verification.
Check out our latest video where Olivier talks about Remote Gate Access Control in detail:
Biometric access control:
Your unique biometric traits become your access badge! Your fingerprint, palm veins, facial features, and even your iris patterns. Biometric access control devices authenticate and authorize individuals at your premises, not just for the main gate, but for doors, facilities, or even devices across different sites.
Biometric access control eliminates the hassle of carrying badges, and it cannot be forged or stolen! These digital logs record all entry and exit events. If you are looking for a high degree of security for high foot traffic, then this access control technology offers many benefits.
Mobile access control:

Mobile access control is also called smartphone access. With smartphones, you carry the world around with you, so why not control access with your phone? Mobile credential access is fast, reliable, and easy.
This app-based entry also offers two-factor authentication. The good news is that employees save on badge purchase and implementation costs. Everything is managed in the cloud. Almost all running iOS or Android smartphones are compatible, and you can even use your Apple smartwatch for this mobile-based entry system.
Conclusion:
Badge access control systems solve a real, everyday problem: uncontrolled access. They replace fragile physical keys with structured, trackable, and scalable entry management across buildings, departments, and sites.
At their best, badge systems deliver speed, convenience, and visibility. You know who entered, where, and when. You can assign permissions in seconds and revoke them just as fast. For most organizations, that alone is a major upgrade.
But badges verify credentials, not people. They can be shared, misused, or bypassed through behaviors like tailgating. That’s where many systems fall short.
The smart move is not to choose between badge access and something else. It’s layering. Combine badge systems with video verification, AI analytics, or biometric checks to close the gaps.
Contact us today for a customized security solution for your business.





